Critical Ransomware Patch: This is not a test.

The IT systems of around 40 NHS organizations across the UK have been affected by a ransomware attack. Non-emergency operations have been suspended and ambulances are being diverted as a result of the attack.
Non-health focused organizations around the world are also being affected, including Spanish telecommunications firm Telefonica which reported a serious issue affecting its internal network as a result of a cyberattack earlier today. The strain is called “Wanna Decrypt0r” which asks $300 from victims to decrypt their computers.
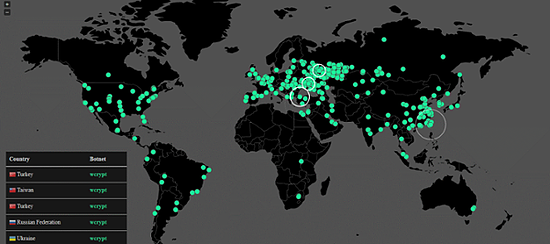
Bleepingcomputer said: “Whoever is behind this ransomware has invested heavy resources into Wana Decrypt0r’s operations. In the few hours this ransomware has been active, it has made many high-profile victims all over the world. According to Avast security researcher Jakub Kroustek, Wana Decrypt0r made over 57,000 victims in just a few hours.
The ransomware’s name is WCry, but is also referenced online under various names, such as WannaCry, WannaCrypt0r, WannaCrypt, or Wana Decrypt0r. As everybody keeps calling it “Wana Decrypt0r,” this is the name we’ll use in this article, but all are the same thing, which is version 2.0 of the lowly and unimpressive WCry ransomware that first appeared in March.”
Sky News Technology Correspondent Tom Cheshire described the attack as “unprecedented”. The ransomware appears to use NSA 0-day ETERNALBLUE and DOUBLEPULSAR exploits which were made public earlier this year by a group calling itself the Shadow Brokers.
Looks like initial infection vector is a phishing/macro email.
According to CrowdStrike’s vice president of intelligence Adam Meyers, the initial spread of WannaCry is coming through spam, in which fake invoices, job offers and other lures are being sent out to random email addresses. Within the emails is a .zip file, and once clicked that initiates the WannaCry infection.
But the most concerning aspect of WannaCry is its use of the worm-like EternalBlue exploit. “This is a weapon of mass destruction, a WMD of ransomware. Once it gets into an unpatched PC it spreads like wildfire,” he told Forbes. “It’s going through financials, energy companies, healthcare. It’s widespread.”
Given the malware is scanning the entire internet for vulnerable machines, and as many as 150,000 were deemed open to the Windows vulnerability as of earlier this month, WannaCry ransomware explosion is only expected to get worse over the weekend.
If you can, apply this patch immediately.
In the mean time, harden yourselves against this threat and ensure that all systems are fully patched with the “MS17-010” security update (link below) and remind all staff to Think Before They Click when they receive any out of the ordinary emails. technet.microsoft.com